This toolkit has been designed by researchers from Ruhr-Universität Bochum in Germany for testing printers against various known vulnerabilities, allowing attackers to capture or manipulate print jobs.
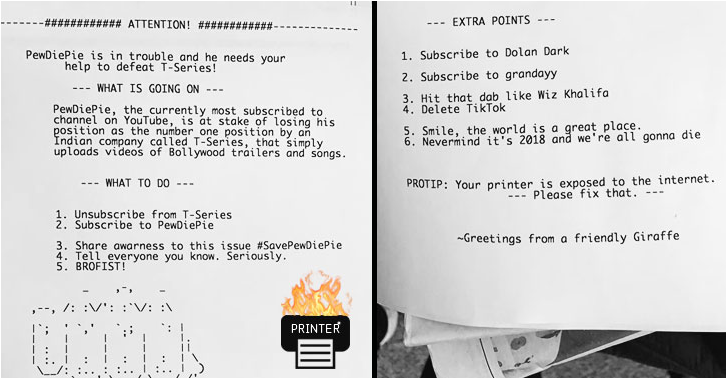
How did the hacker find these vulnerable devices?
He used Shodan, search engine for Internet-connected devices, to discover the list of vulnerable printers with port 9100 open.






![[Securiday 2018] End User Protection](https://digitalys-mag.net/wp-content/uploads/2018/04/securiday18_conf.jpg)

![Détective Conan : les épisodes de l’histoire principale triées [part 1]](https://digitalys-mag.net/wp-content/uploads/2016/08/Meitantei.Conan_.full_.1913572.jpg)

![[Warning] Une faille critique dans tous les jeux Blizzard permettra aux Hackers de détourner des millions de PC](https://digitalys-mag.net/wp-content/uploads/2018/01/X1NH71Z11PTZ1508884994858.jpg)